A Russian threat actor known for its malware campaigns has reappeared in the threat landscape with yet another attack leveraging COVID-19 as phishing lures, once again indicating how adversaries are adept at repurposing the current world events to their advantage.
Linking the operation to a sub-group of APT28 (aka Sofacy, Sednit, Fancy Bear, or STRONTIUM), cybersecurity firm Intezer said the pandemic-themed phishing emails were employed to deliver the Go version of Zebrocy (or Zekapab) malware.
The cybersecurity firm told The Hacker News that the campaigns were observed late last month.
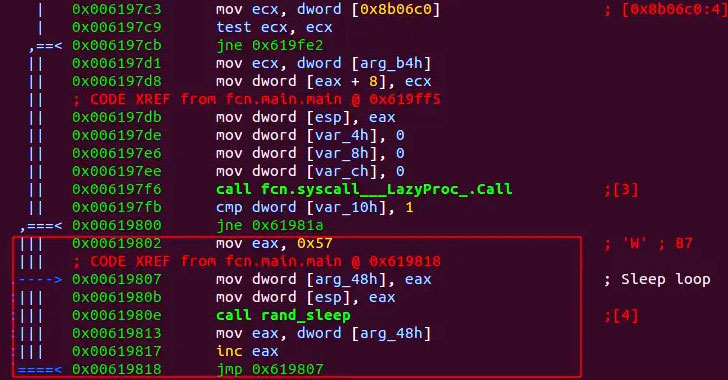
Zebrocy is delivered primarily via phishing attacks that contain decoy Microsoft Office documents with macros as well as executable file attachments.
First spotted in the wild in 2015, the operators behind the malware have been found to overlap with GreyEnergy, a threat group believed to be the successor of BlackEnergy aka Sandworm, suggesting its role as a sub-group with links to Sofacy and…